Performing a Custom Installation
You can install Zerto providing specific details including the ports that will be used by Zerto and full contact details.
Before you Begin:
To perform a custom install of Zerto:
1. Run the Zerto installation executable for Amazon Web.
Note: If the required version of Microsoft .NET Framework is not installed, you are prompted to install the required version of .NET Framework, which is included as part of the Zerto installation package. After .NET is installed the machine automatically restarts and the Zerto installation begins.
2. Follow the wizard through the installation until the dialog for the Installation Type and select the Custom Installation option.
3. Click Next.
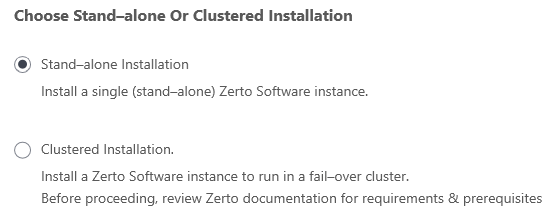
The Choose Stand-alone Or Clustered Installation window appears.
4. Select Stand-alone Installation, then click Next.
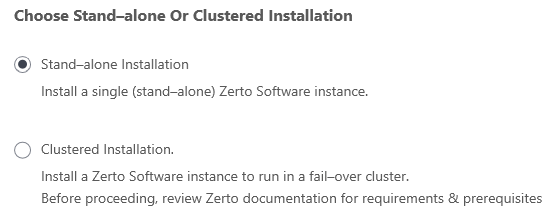
The Windows Service User dialog is displayed.
5. Select either Local System account or This account:
■ Local System account: Use the Local System account to run the Zerto Virtual Manager service, which is installed as part of Zerto. The Local System account has unrestricted access to local resources.
■ This account: Use a specific account as the user account to run the Zerto Virtual Manager service, which is installed as part of Zerto. The account must have unrestricted access to local resources.
■ Password: The password to use to run the service under the specified account.
■ Confirm Password: Confirmation of the password.
6. Click NEXT.
The Database Type dialog is displayed.
Information required by Zerto is stored in a database embedded in the Zerto Virtual Manager. This information includes details of the site where the Zerto Virtual Manager is installed, details of the Virtual Replication Appliance and the volumes it uses, and points-in-time recorded for recovery purposes. By default an embedded SQL-based database is used, but you can use an externally managed database, either Microsoft SQL Server or SQL Server Express.
Note: Protection and recovery can only be performed when the database is running. Therefore, if you use an external database and it is down for any reason, protection and the possibility of recovery ceases.
7. To use the embedded database, leave the default, or select the option to connect to an external Microsoft SQL Server database.
Zerto recommends using SQL Server when a site has more than 40 hosts that have virtual machines that need protecting, and the site has more than 400 virtual machines that need protecting.
If you select the external database option, the SQL Server Authentication section is enabled.
a) Enter the following details to enable access to the SQL Server database:
■ Server Name: The domain name and server instance to connect to, with the format <server_name>\<instance_name> or <Server_IP>\<instance_name>
b) Specify one of the following authentication options:
■ Windows Authentication: Use Windows authentication. This option is only enabled if a specific service user account was specified in the previous Windows Service User dialog, in which case the service account name and password are used.
■ SQL Server Authentication: Use SQL Server authentication.
Username: The user name for the SQL Server database.
Password: A valid password for the given user name.
c) When you select SQL Server authentication and enter a user name and password, click TEST AUTHENTICATION, which is displayed.
The installer checks whether it can connect to the specified database with the specified username and password. You can only continue when the authentication is successful.
8. Click NEXT.
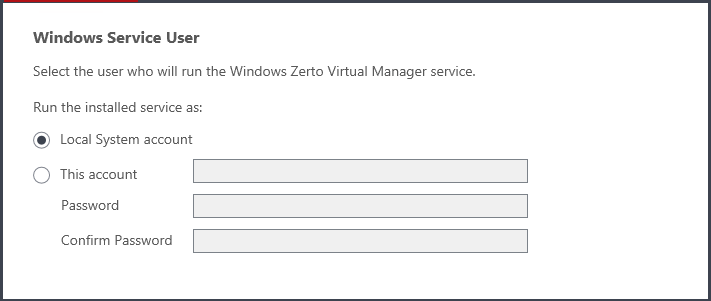
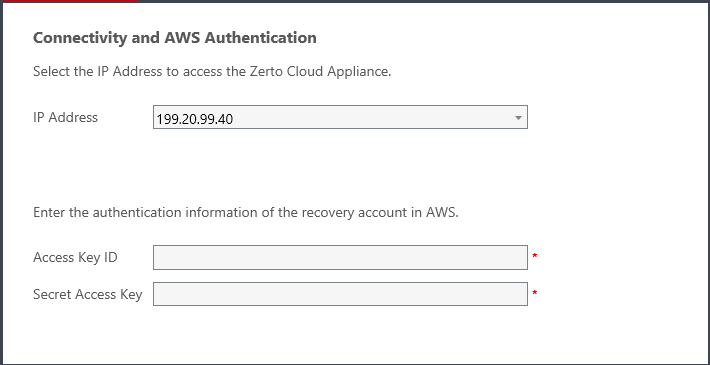
The Connectivity and AWS Authentication dialog is displayed.
9. Specify the following:
■ IP Address: The IP address or host name of the machine on which you are installing the Zerto Cloud Appliance. The protected site accesses the recovery site using this IP.
■ Access Key ID: A unique identifier that is associated with a secret access key.
■ Secret Access Key: A key that is used with the access key ID.
AWS uses the access key ID and secret access key to identify the sender, ensure that the sender is authorized to make the request, and to prevent the request from being altered.
10. Click NEXT.
The Zerto Virtual Manager Site Details dialog is displayed. Enter the site details:
Site Name: | (Optional) A name to identify the site. This name is displayed in the Zerto User Interface |
Site Location: | (Mandatory) Information such as the address, or name of the site to identify it. |
Contact Name: | (Mandatory) The name of the person to contact if a need arises. |
Contact Email: | (Optional) The email address to contact if a need arises. |
Contact Phone: | (Optional) The phone number to contact if a need arises. |
Click NEXT.
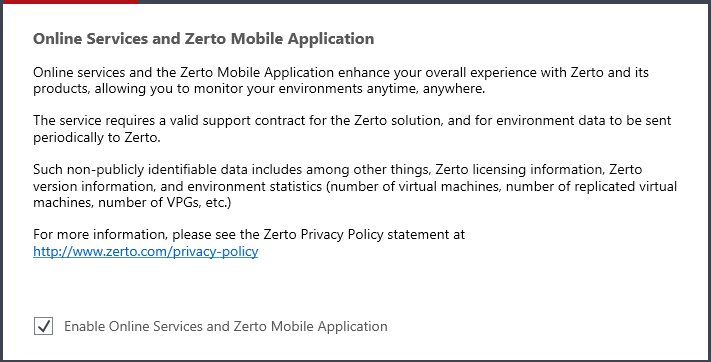
The Online Services and Zerto Mobile Application dialog is displayed.
The Online Services and Zerto Mobile Application are enabled by default. These services can be disabled by unchecking Enable Online Services and Zerto Mobile Application.
11. Click NEXT.
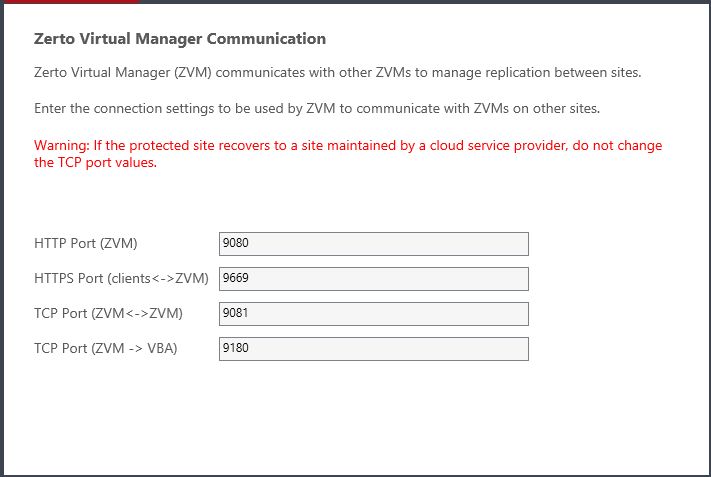
The Zerto Virtual Manager Communication dialog is displayed.
Port Description Parameter | Default Port Number | Communication Direction | Between... | Comments |
HTTP Port (ZVM) | 9080 | Inbound | Zerto Virtual Manager - and - Zerto internal APIs, and Cmdlets | |
HTTPS Port (clients<->ZVM) | 9669 | Inbound | Zerto User Interface - and - Zerto Virtual Manager | |
TCP Port (ZVM<->ZVM) | 9081 | Inbound and outbound | Zerto Virtual Manager - and - Zerto Virtual Manager | If you change the value, when pairing sites, use the TCP port value you specify here. Pairing the sites is described in “Pairing an AWS Site”, on page 17. |
TCP Port (ZVM->VBA) | 9180 | Inbound and outbound | Zerto Virtual Manager - and - Virtual Backup Appliance (VBA) | |
12. Click NEXT.
The Validation dialog is displayed. The installation checks that the installation can proceed successfully.
13. After you see that Zerto can be installed successfully, click RUN and continue to the end of the installation.
The installation creates a bucket on S3 with a name like “zerto-<GUID>”.
14. If you intend managing your disaster recovery from this machine, you can select to open the Zerto Virtual Manager (ZVM) Interface at the end of the installation, logging in with the user name and password for the AWS instance on which you installed the Zerto Virtual Manager. In this user interface you set up Zerto, as described in
“Initial Configuration”, on page 17.
15. You must exclude the following folders from antivirus scanning:
Zerto Virtual Replication |
%ProgramData%\Zerto\Data\zvm_db.mdf |
C:\Program Files\Zerto\Zerto Virtual Replication\Zerto.Zvm.Service.exe |
C:\Program Files\Zerto\Zerto Virtual Replication\Zerto.Vba.VbaService.exe |
C:\Program Files\Zerto\Zerto Virtual Replication\Zerto Online Services Connector\Zerto.Online.Services.Connector.exe |
C:\Program Files\Zerto\Zerto Virtual Replication\Embedded DB Manager Service\Zerto.LocalDbInstanceManagerService.exe |
Failure to do so may lead to the Zerto Virtual Replication folder being incorrectly identified as a threat and in some circumstances corrupt the Zerto Virtual Replication folder.
16.